Currently there are many cyber security vendors out there that provide solutions that offer "AI" (artificial intelligence) or "ML" (machine learning) without specifying what that actually entails within their point solution. This has created some aversion among cyber security professionals against vendors that blatantly use this type of "marketing lingo".
Some of these vendors actually provide some shape of form of a "narrow AI" that is generally (for example) following a limited logic:
- Detect IP -> Classify as a threat -> block IP on firewall
- Detect endpoint -> Classify as a threat -> isolate endpoint
- Detect User -> Classify as a threat -> disable user on IAM solution
Generally all AI that only pertains to cyber security risk is a narrow A.I., but in these cases it's even more narrow as of the limited closed OODA (observe, orient, decide and ACT) loop provided by the solution. Besides that most vendors are just using their "point solution" as the AI and doesn't take into account the wider landscape of "AI" opportunities within the cyber security solution stack of the organization.
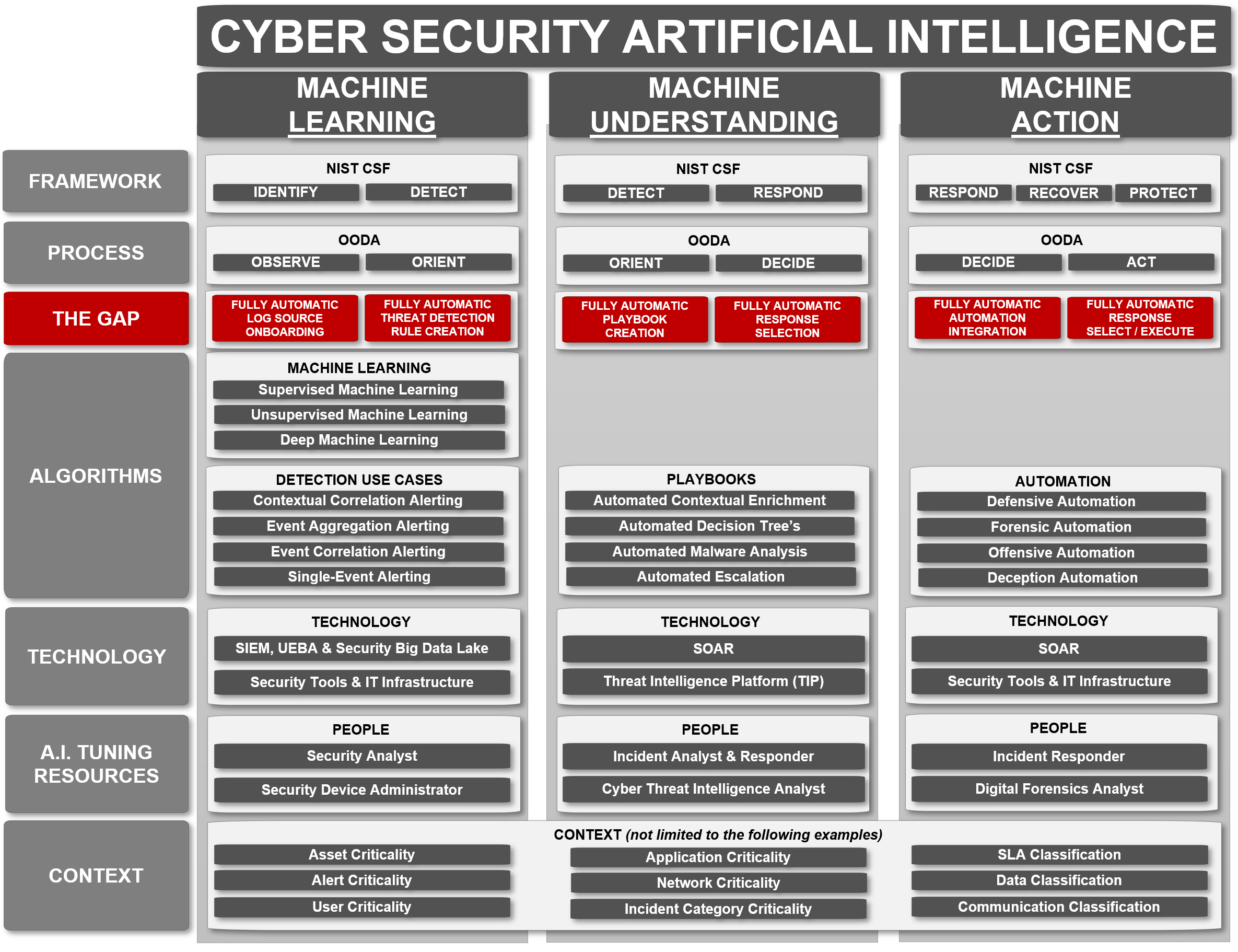
This made me put together an architectural diagram trying to fit in a series of solutions and concepts that would be able to provide a more wider foundation for the fully automated "OODA" loop that AI is trying to achieve within the cyber security space.
The following diagram highlights the gaps currently within this potential future target architecture following the general definition of what "AI" supposed to do.
Artificial intelligence (AI) refers to the simulation of human intelligence in machines that are programmed to think like humans and mimic their actions.
Currently there are the following gaps in the CSOC context regarding the implementation of this form of AI, as there is no out-of-the-box solution that can do all of the following:
- NO FULLY AUTOMATIC LOG SOURCE ONBOARDING
- NO FULLY AUTOMATIC THREAT DETECTION RULE CREATION
- NO FULLY AUTOMATIC PLAYBOOK CREATION
- NO FULLY AUTOMATIC RESPONSE SELECTION
- NO FULLY AUTOMATIC AUTOMATION INTEGRATION
- NO FULLY AUTOMATIC RESPONSE SELECT / EXECUTE
Because of these technologies will take a while to develop the move to this targeted architecture is accelerated by the move to the cloud as this will provide more standardized closed loop environments and with the drive for API-centric design in all application/systems nowadays (allowing for either extraction of events and actions on the application/system) we are getting more close to this type of environment.
Conclusion:
Use this diagram as a target reference architecture, setup your CSOC architecture to allow and measure on increased micro implementations of closed "OODA" loops to accelerate getting to this targeted AI vision within the CSOC in the long term. With this in mind we might be able to use a series of "fully automated OODA loops" stacked upon each other, to make it look like as something that closely resembles the "Cyber Security AI" architecture.