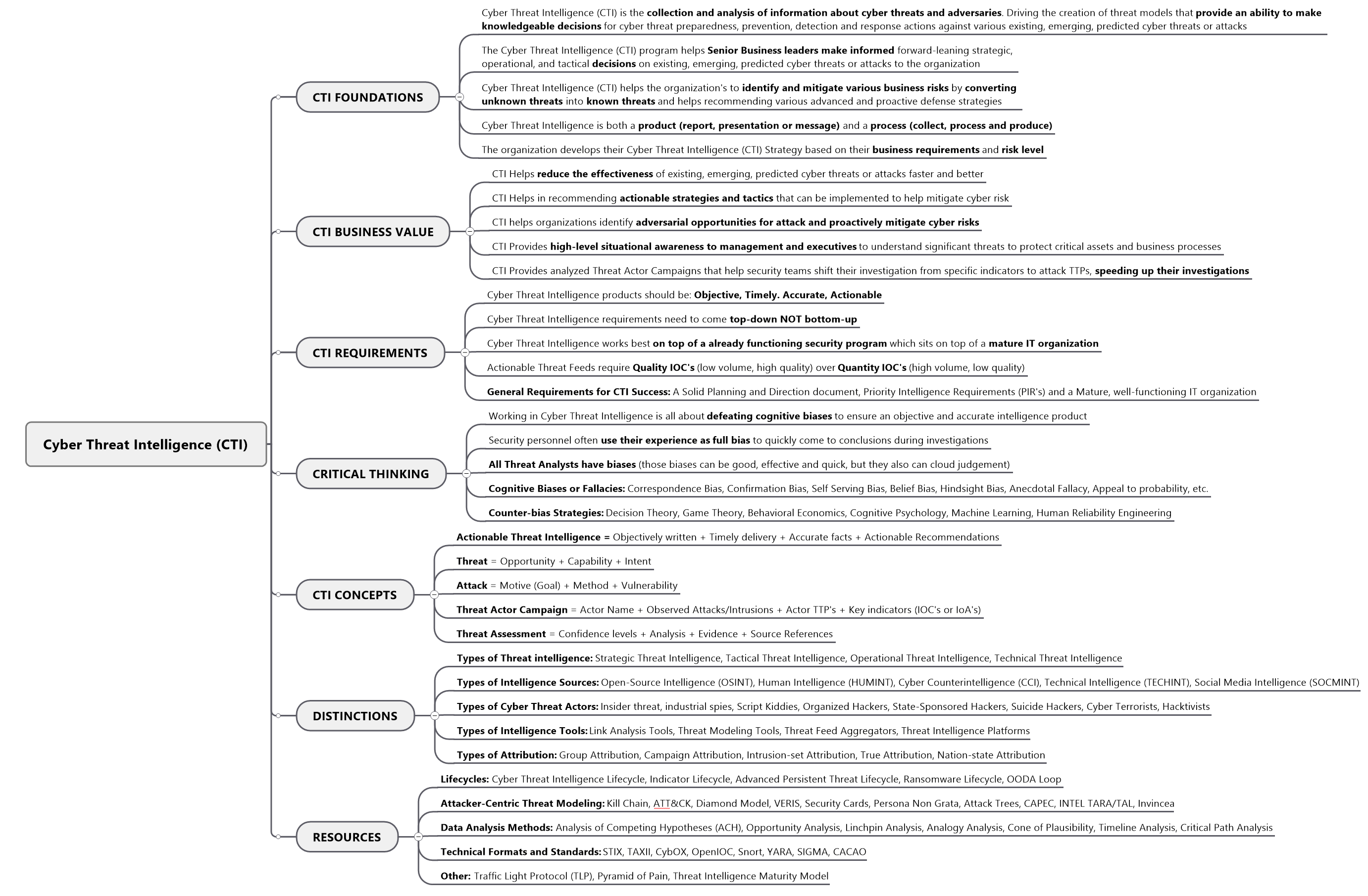
I have studied the SANS GCTI and EC-Council CTIA Cyber Threat Intelligence (CTI) certificates quite extensively and have attempted to summarize the 20% of the knowledge that would provide 80% of the domain knowledge coverage. Hopefully it's of value to someone not familiar on the topic or someone that is a seasoned professional on the topic.
CTI FOUNDATIONS
- Cyber Threat Intelligence (CTI) is the collection and analysis of information about cyber threats and adversaries. Driving the creation of threat models that provide an ability to make knowledgeable decisions for cyber threat preparedness, prevention, detection and response actions against various existing, emerging, predicted cyber threats or attacks
- The Cyber Threat Intelligence (CTI) program helps Senior Business leaders make informed forward-leaning strategic, operational, and tactical decisions on existing, emerging, predicted cyber threats or attacks to the organization
- Cyber Threat Intelligence (CTI) helps the organization's to identify and mitigate various business risks by converting unknown threats into known threats and helps recommending various advanced and proactive defense strategies
- Cyber Threat Intelligence is both a product (report, presentation or message) and a process (collect, process and produce)
- The organization develops their Cyber Threat Intelligence (CTI) Strategy based on their business requirements and risk level
CTI BUSINESS VALUE
- CTI Helps reduce the effectiveness of existing, emerging, predicted cyber threats or attacks faster and better
- CTI Helps in recommending actionable strategies and tactics that can be implemented to help mitigate cyber risk
- CTI helps organizations identify adversarial opportunities for attack and proactively mitigate cyber risks
- CTI Provides high-level situational awareness to management and executives to understand significant threats to protect critical assets and business processes
- CTI Provides analyzed Threat Actor Campaigns that help security teams shift their investigation from specific indicators to attack TTPs, speeding up their investigations
CTI REQUIREMENTS
- Cyber Threat Intelligence products should be: Objective, Timely. Accurate, Actionable
- Cyber Threat Intelligence requirements need to come top-down NOT bottom-up
- Cyber Threat Intelligence works best on top of a already functioning security program which sits on top of a mature IT organization
- Actionable Threat Feeds require Quality IOC's (low volume, high quality) over Quantity IOC's (high volume, low quality)
- General Requirements for CTI Success: A Solid Planning and Direction document, Priority Intelligence Requirements (PIR's) and a Mature, well-functioning IT organization
CRITICAL THINKING
- Working in Cyber Threat Intelligence is all about defeating cognitive biases to ensure an objective and accurate intelligence product
- Security personnel often use their experience as full bias to quickly come to conclusions during investigations
- All Threat Analysts have biases (those biases can be good, effective and quick, but they also can cloud judgement)
- Cognitive Biases or Fallacies: Correspondence Bias, Confirmation Bias, Self Serving Bias, Belief Bias, Hindsight Bias, Anecdotal Fallacy, Appeal to probability, etc.
- Counter-bias Strategies: Decision Theory, Game Theory, Behavioral Economics, Cognitive Psychology, Machine Learning, Human Reliability Engineering
CTI CONCEPTS
- Actionable Threat Intelligence = Objectively written + Timely delivery + Accurate facts + Actionable Recommendations
- Threat = Opportunity + Capability + Intent
- Attack = Motive (Goal) + Method + Vulnerability
- Threat Actor Campaign = Actor Name + Observed Attacks/Intrusions + Actor TTP's + Key indicators (IOC's or IoA's)
- Threat Assessment = Confidence levels + Analysis + Evidence + Source References
DISTINCTIONS
- Types of Threat intelligence: Strategic Threat Intelligence, Tactical Threat Intelligence, Operational Threat Intelligence, Technical Threat Intelligence
- Types of Intelligence Sources: Open-Source Intelligence (OSINT), Human Intelligence (HUMINT), Cyber Counterintelligence (CCI), Technical Intelligence (TECHINT), Social Media Intelligence (SOCMINT)
- Types of Cyber Threat Actors: Insider threat, industrial spies, Script Kiddies, Organized Hackers, State-Sponsored Hackers, Suicide Hackers, Cyber Terrorists, Hacktivists
- Types of Intelligence Tools: Link Analysis Tools, Threat Modeling Tools, Threat Feed Aggregators, Threat Intelligence Platforms
- Types of Attribution: Group Attribution, Campaign Attribution, Intrusion-set Attribution, True Attribution, Nation-state Attribution
RESOURCES
- Lifecycles: Cyber Threat Intelligence Lifecycle, Indicator Lifecycle, Advanced Persistent Threat Lifecycle, Ransomware Lifecycle, OODA Loop
- Attacker-Centric Threat Modeling: Kill Chain, ATT&CK, Diamond Model, VERIS, Security Cards, Persona Non Grata, Attack Trees, CAPEC, INTEL TARA/TAL, Invincea
- Data Analysis Methods: Analysis of Competing Hypotheses (ACH), Opportunity Analysis, Linchpin Analysis, Analogy Analysis, Cone of Plausibility, Timeline Analysis, Critical Path Analysis
- Technical Formats and Standards: STIX, TAXII, CybOX, OpenIOC, Snort, YARA, SIGMA, CACAO
- Other: Traffic Light Protocol (TLP), Pyramid of Pain, Threat Intelligence Maturity Model